IT security. What do we need to know?
Published on 18 December 15
1
1
Bruce Schneier predicts a huge cyberattack on the USA.
o tell you the truth the attack, won't hit the voting system and may not include the presidential elections, but rather the enticement for programmers is excessively extraordinary, even in state and neighborhood races, said Schneier, a PC security pioneer and long-term analyst.
"There will be hacks that influence governmental issues in the United States," Schneier said. Aggressors might break into hopefuls' sites, email or online networking records to reveal material the battles don't need open, he said. As a result everybody should be aware of IT security.
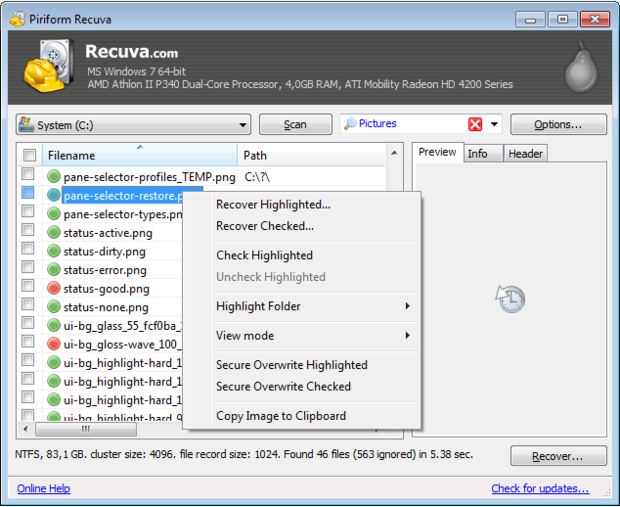
Task 1: Perform computerized crime scene investigation by recouping erased records
Computerized crime scene investigation is a branch of criminological science committed to information recuperation and examination of tech gadgets. Recovering erased information is one noteworthy part of a computerized measurable expert's employment.
Recouping erased documents from a PC or capacity gadget can give you an essence of computerized crime scene investigation, while likewise demonstrating to you firsthand why information security is so imperative—a criminal could do likewise to get delicate data off a stolen gadge . There are many free resources such as Recuva and DiskDrill.
Task 2: Use PGP encryption for securing email and sharing records
As you likely know, encryption has real influence in information security. Exceedingly touchy information, for example, Social Security numbers, charge card subtle elements and archives containing competitive innovations, ought to be encoded,protect your britishessaywriter account, amid the information's transmission and in addition away and reinforcement.
There are a wide range of encryption sorts and items accessible. PGP (Pretty Good Privacy) encryption is broadly utilized for safely trading email messages and documents with others.
PGP encryption utilizes an open and private key plan. When you need to send PGP encoded messages or documents to somebody, you should first get their open key to scramble the information. Whenever scrambling, you pick whom you'd like to have the capacity to decode the information, and just those you assign can do as such. At the point when those predetermined individuals get the information encoded with their open key, they utilize their private key to decode it.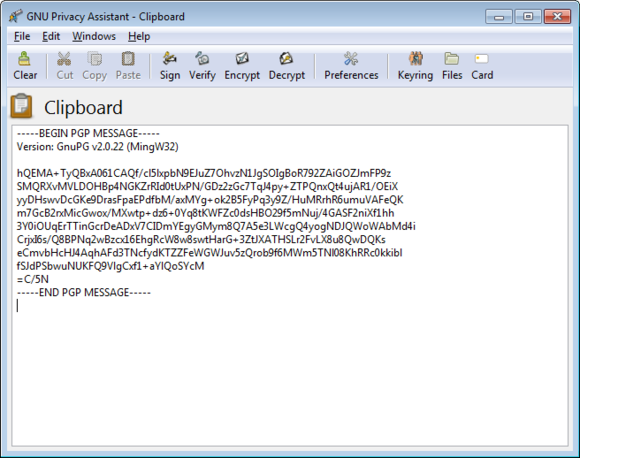
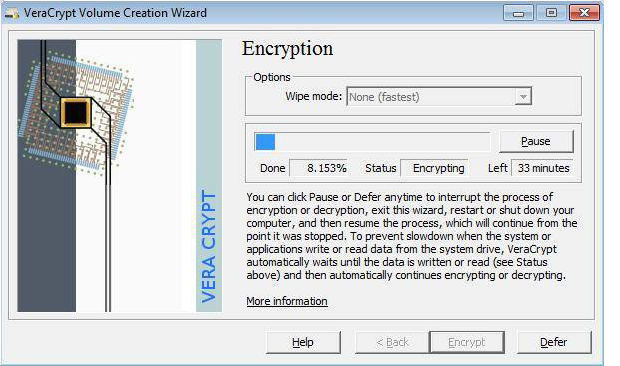
Task 3:Use document or full protection.
Record and full-disk encryption are most valuable for securing information that a solitary individual will store, get to, exchange or move down. (Sharing encoded records between different individuals, utilizing PGP, was secured in the past undertaking.)
Record encryption is helpful when you have to keep a select number of documents or envelopes encoded. Full-disk encryption encodes all documents on a PC or capacity gadget, which guarantees that no information will be recoverable by a criminal if the gadget is lost or stolen.
You could use VeraCrypt for different types of encryption on Windows, Mac OS X and Linux.
This blog is listed under
IT Security & Architecture
Community
Related Posts:
Cyber security
IT security
You may also be interested in
Share your perspective

Share your achievement or new finding or bring a new tech idea to life. Your IT community is waiting!

 Karl
Karl







Nice one, I think it is the best article at the https://www.mytechlogy.com